Imagine you put your funds in a protocol expecting a good return, but 1–2 months down the line, you find out that the funds are lost due to a security breach just because the protocol did not keep up with the attack vectors or was inefficient in monitoring the attack, where would that leave you?
To save yourself from such unfortunate circumstances, we advise you to always put only work with the protocols which take security very seriously, and in that matter, security is not a one-time investment. It involves continuous advancement and development based on the ever-evolving threat landscape.
In this blog, we are going to learn about why continuous monitoring is one of the most crucial parts of keeping the protocols safe and how it helps us secure Web3, Let’s start one by one.
Protection from Evolving threats
As technology advances, so does the attacking strategies and threats faced by Web3. Cybercriminals use sophisticated tools and use the latest technologies like automation, artificial intelligence etc. The problem arises when the protocol or the projects are not putting effort into keeping themselves ahead of the attackers.
Enterprises should always take every measure to create a secure environment for users and should always try to anticipate and prepare for potential cybersecurity vulnerabilities. These cybersecurity solutions include regular monitoring systems, identifying vulnerabilities and preventing data and security breaches.
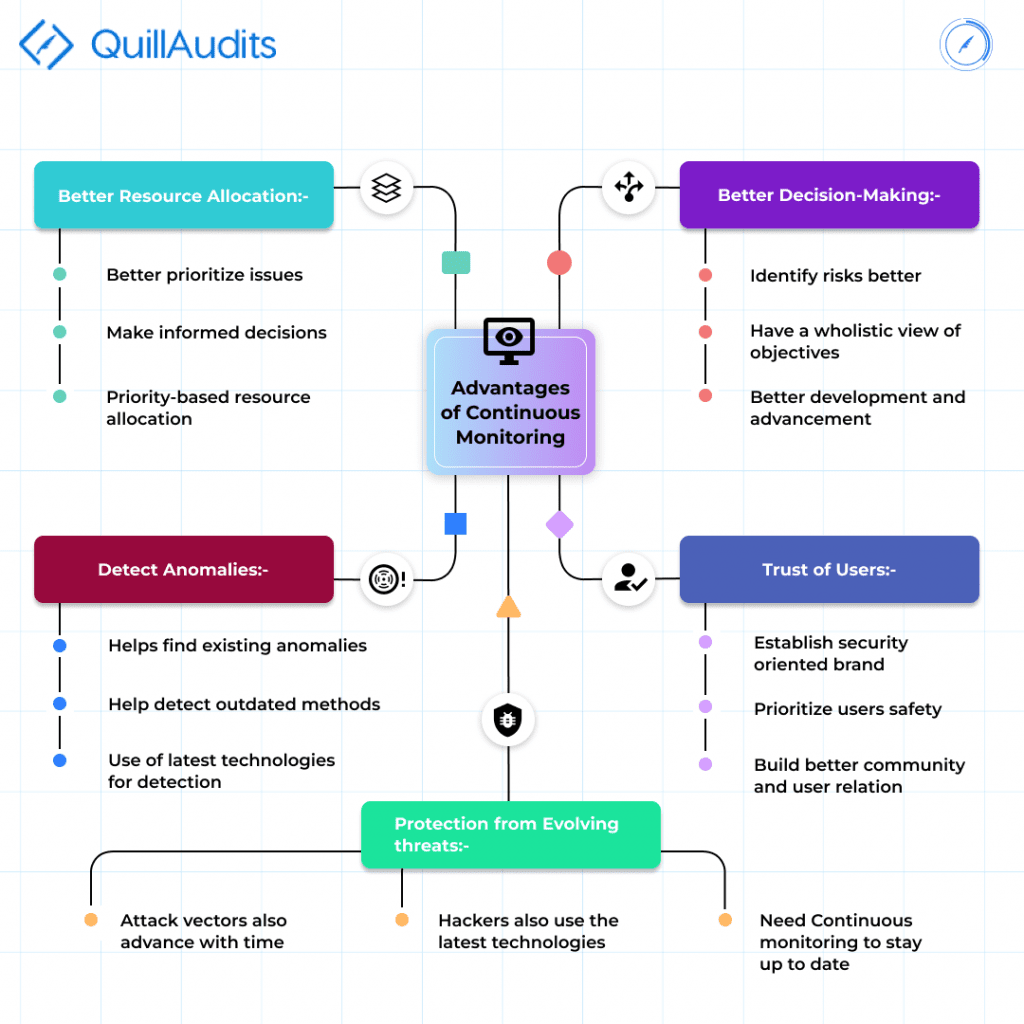
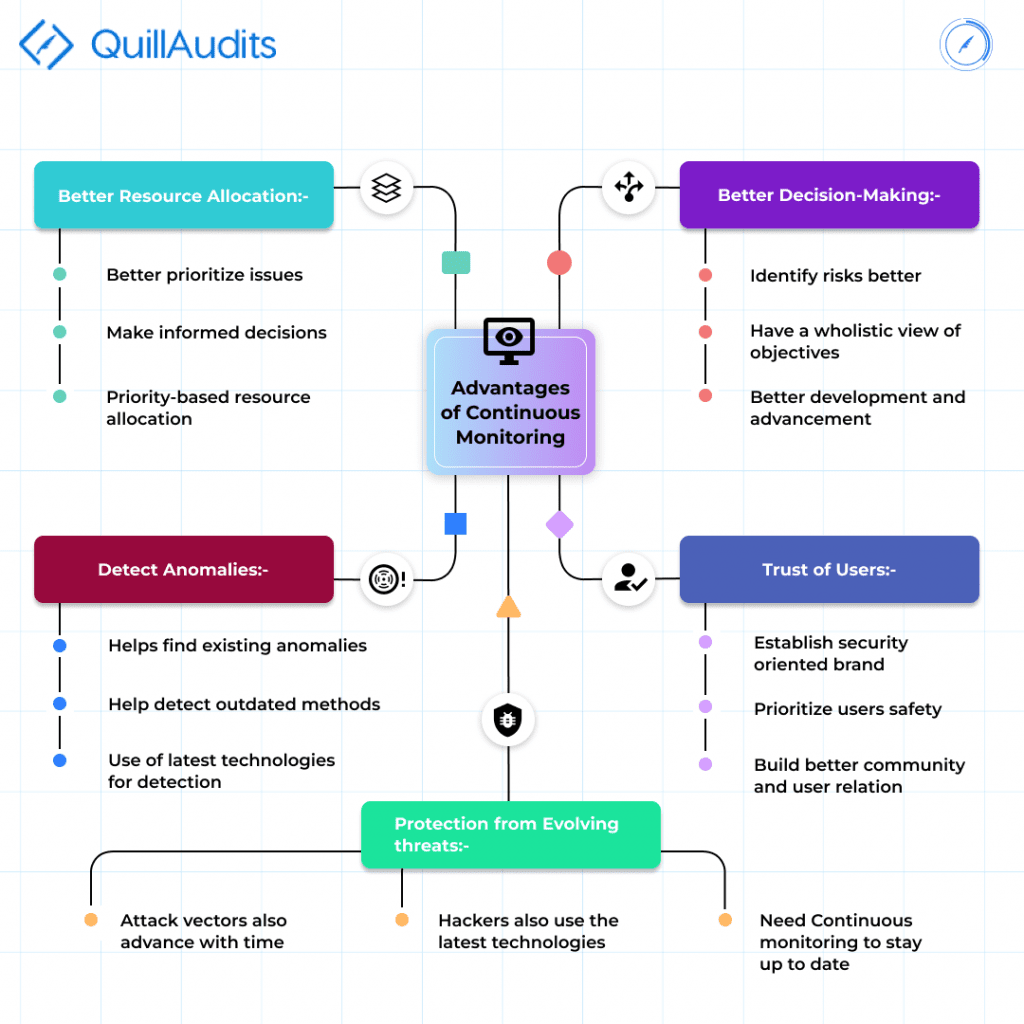
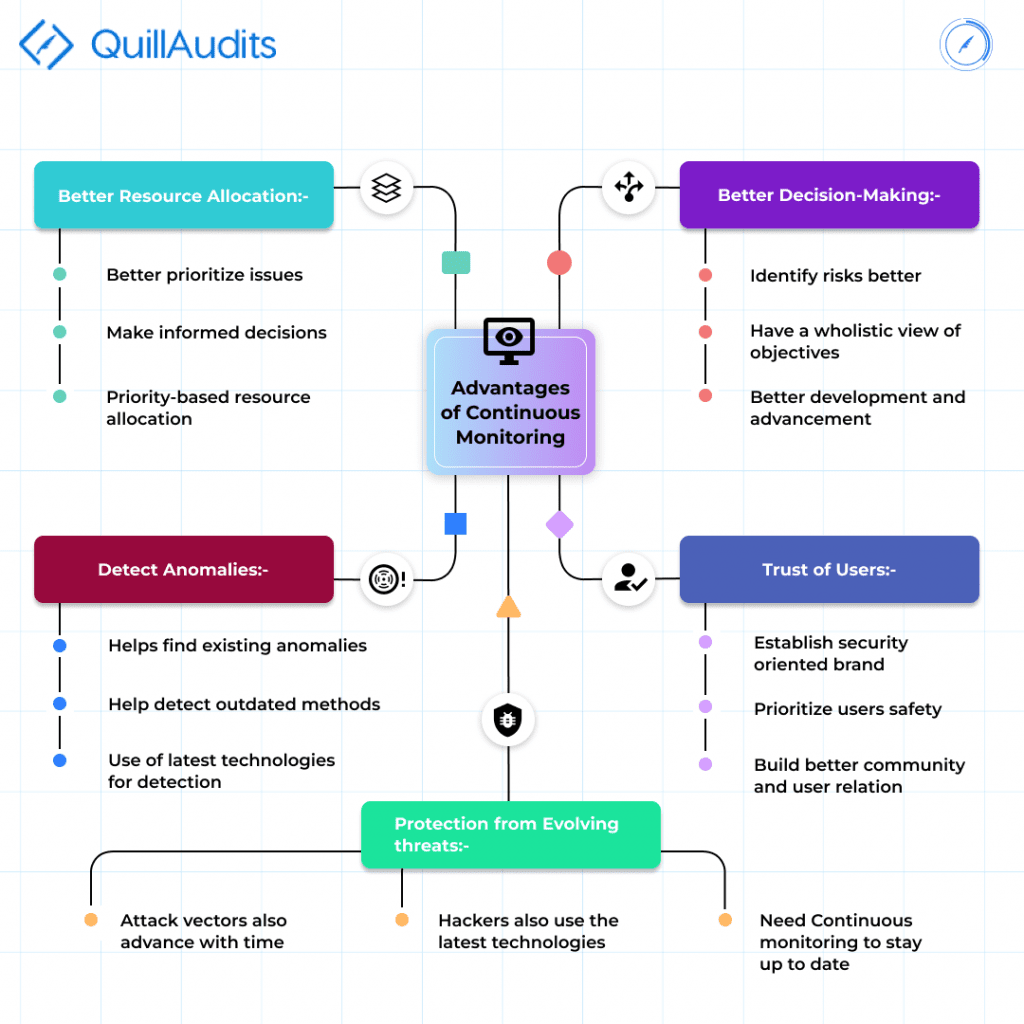
Better Resource Allocation
When a flaw or a problem is found in a bridge under construction, based on how severe and important the problem is, human resources are allocated to it. If the problem is severe, the resources allocated tend to be high, and if the problem is not that significant low resources can be allocated. Still, the problem can be overcome.
The same phenomenon can be noticed in Web3 Enterprises. When we continuously monitor our Web3 Applications, based on the issues we find, we can allocate suitable resources for the issue and make a more efficient system of tackling the problems on a priority basis. Thus constant monitoring and tracking help build a robust cybersecurity program.
Detects Anomalies
When we are inclined towards continuous monitoring, we are not only guiding ourselves from the attacks but also constantly looking for any flaws any anomalies present at our end. To do this, many technologically advanced tools are made use of. These tools mainly have data observability, artificial intelligence or machine learning as their backbone.
Better Decision-Making Capability
Better decision-making capability comes with a highly secure business. The constant monitoring helps us identify the risks which the enterprise is facing, and this information becomes very crucial when we are at a decision-making stage. It is clear that the more information and knowledge we have about the weakness of our system, the better decision we can make.
As decisions are a really important factor dictating the success of our protocol and the direction the enterprise goes, continuous monitoring is thus directly related to better development and advancement of the enterprise.
Trust of Users
As the users understand the need and importance of cybersecurity, the more the users are going to demand it, and slowly and steadily, the one providing the better cybersecurity practices and safety is going to attract more users and build a better trust relationship.
As Web3 advances, there will be different parameters the users will judge its trustability on. The users will understand the need for several security-related essentials like an Audit report, continuous monitoring system, and failure mechanism. Without these, it will be hard for users to put in trust. Thus it becomes crucial to use a continuous monitoring system to provide the user’s needs and safety.
Conclusion
With the ever-advancing attack vectors and new types of attacks making their way into the industry, it is of utmost importance to keep ourselves ready and informed about them. The only way to do that is by employing continuous monitoring to our advantage.
Continuous monitoring provides you with many advantages, as discussed above. In addition to continuous monitoring, we also need to be prepared for the impact in case our protocol gets compromised, and we will learn about that in one of our next blogs, so stay tuned for that.
In addition to continuous monitoring, we also have an amazing facility for smart contract auditing. It is the gateway for users’ trust in the protocol and one of the most crucial parameters in deciding how secure the protocol is. We at QuillAudits are experts in the auditing industry, so pay us a visit on our website and get your project audited today.






















